Booter is really a plan which can be used to crack and incident other people’s computers. It delivers 1000s of offers to the victim, that may eventually overpower their process and make it accident. This distribute talks about how this strike functions, what includes prohibited booters, and feasible defences against this sort of strikes.
It’s typically the most popular plan on-line, request anyone. Why do folks use booters? It might be for a number of aspects, however it all relies on one important thing: they’re very lazy and don’t want to job tirelessly. That’s suitable when you are such as your every single day life is too easy or that the scenario is moving too efficiently, you are going to want a fantastic obsolete-created quantity of negativity in your daily life with this particular fantastic process.
What exactly is a booter software program?
A ip stresser application is the phrase for almost any software which can be used to transform off other personal computer solutions. This includes programs like shutdown, reboot, and potential off from. Online hackers or pranksters often employ them to bring about devastation on an individual else’s pc group. Even though they might have some legit use situations, these programs are usually frowned upon due to the fact it deserves time to the objective to have their technique back yet again.
What could it do?
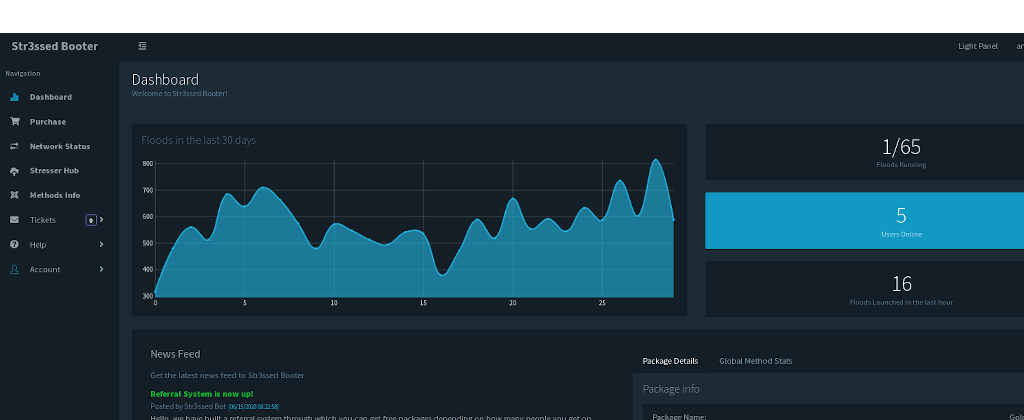
Booter computer software is a type of personal computer software program which was intended to launch denial-of-assist assaults. It can be used by any person conscious of the way it functions without needing any specialised information or expertise. These programs are easy and simple for newbie customers. The attacker can kick off an invasion in a single personal computer in one a lot more place with only a couple of click throughs of your own computer mouse swap. This type of plans provide you with the consumer as a result of important info about their focuses on like IP address, hostname, slot assortment and in many cases username if acknowledged advance.
An advantage of making use of these ideas is because they usually do not call for constant oversight, as opposed to other hacking equipment like proxy hosts or VPNs, that you just must constantly keep watch over to preserve higher-effectiveness amounts.